Mode Help
Administration
Access Control & Permissions
Report and Dataset Access
In Mode's paid plans, Admins can use a combination of Collection permissions and database Connection permissions to control view and edit access to Reports in their Workspace.
To understand why a Workspace member doesn’t have access to a Report, check the database Connection and Collection default access from the Report itself.
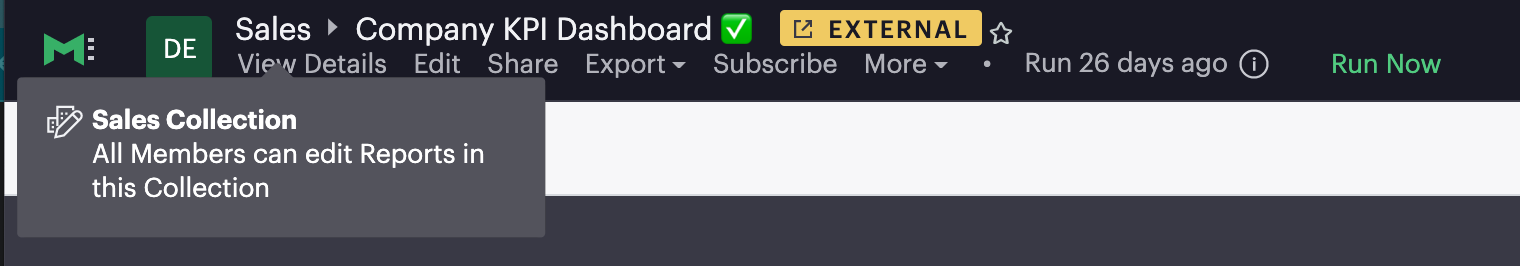
To see the Collection default access level for Workspace members, hover over the Collection name in the Report header.
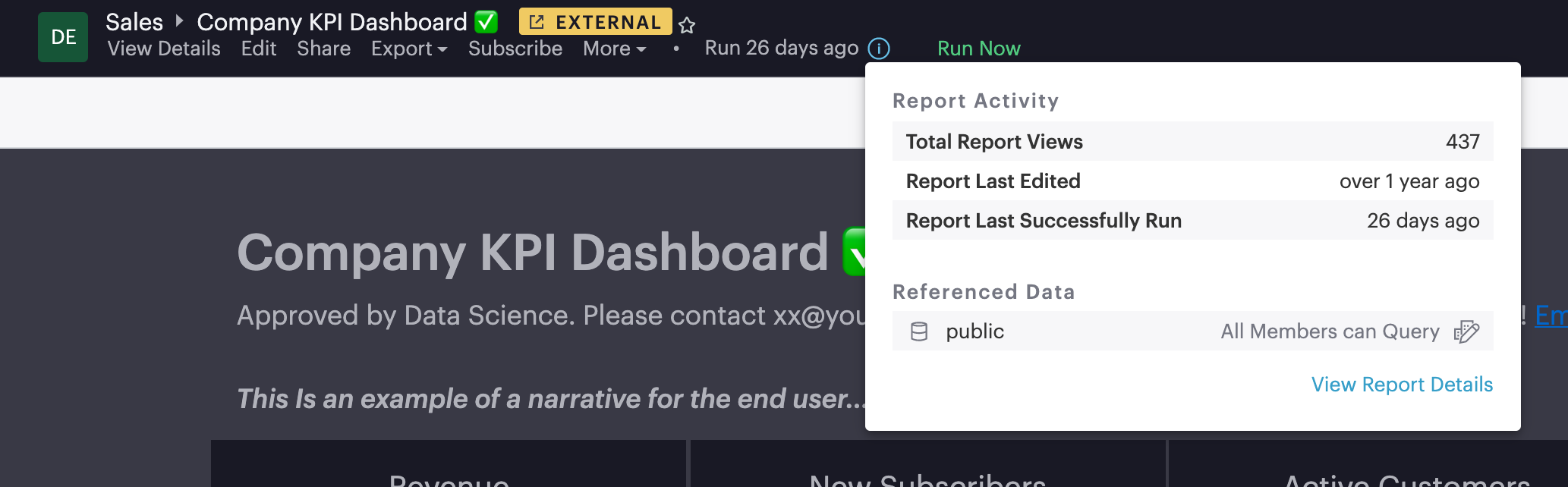
To see all database Connections used in the Report and the default access level for each of the Connections, either click the info icon next to the Run button or navigate to View Details.
These are the permissions that Workspace members need in order to access a Report:
- To edit a Report, Workspace members must have Query permission to all database Connections used in the Report and Edit permission to the Report's Collection
- To view a Report, Workspace members must have View permission to all database Connections used in the Report and View permission to the Report's Collection
- To duplicate a Report, Workspace members must have Query permission to all database Connections used in the Report and at least View permission to the Report's Collection
Create Groups
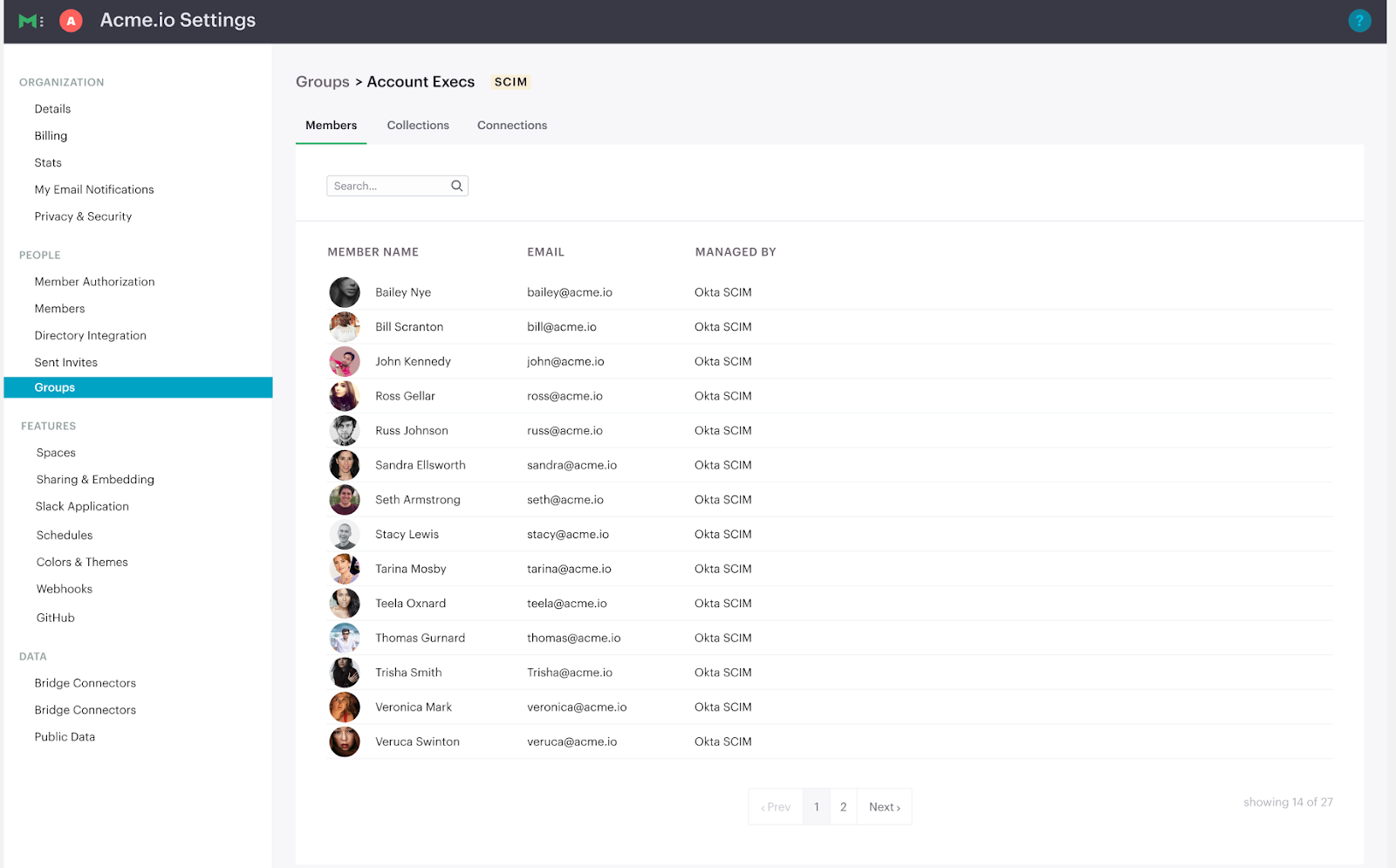
Use Groups to manage access to resources in Mode. By granting an individual user membership to a Group, you grant them access to resources based on their Group membership. Each Group in Mode can be configured with a unique set of permissions. Mode’s permission system gives you the flexibility to change the role of an individual user by adding or removing that user to or from different Groups.
You can create Groups by navigating to Workspace Settings and clicking into the Groups tab. Select a Group from the list to manage its members.
From here, selecting the Collections and Connections tabs will provide visibility into which Collections and Connections a Group can access.
Admins
Admins in Mode have the highest level of access to all resources by default. Only make users Admins if they are authorized to manage all groups, connections, collections and reports in Mode.
Set Up Connection Permissions
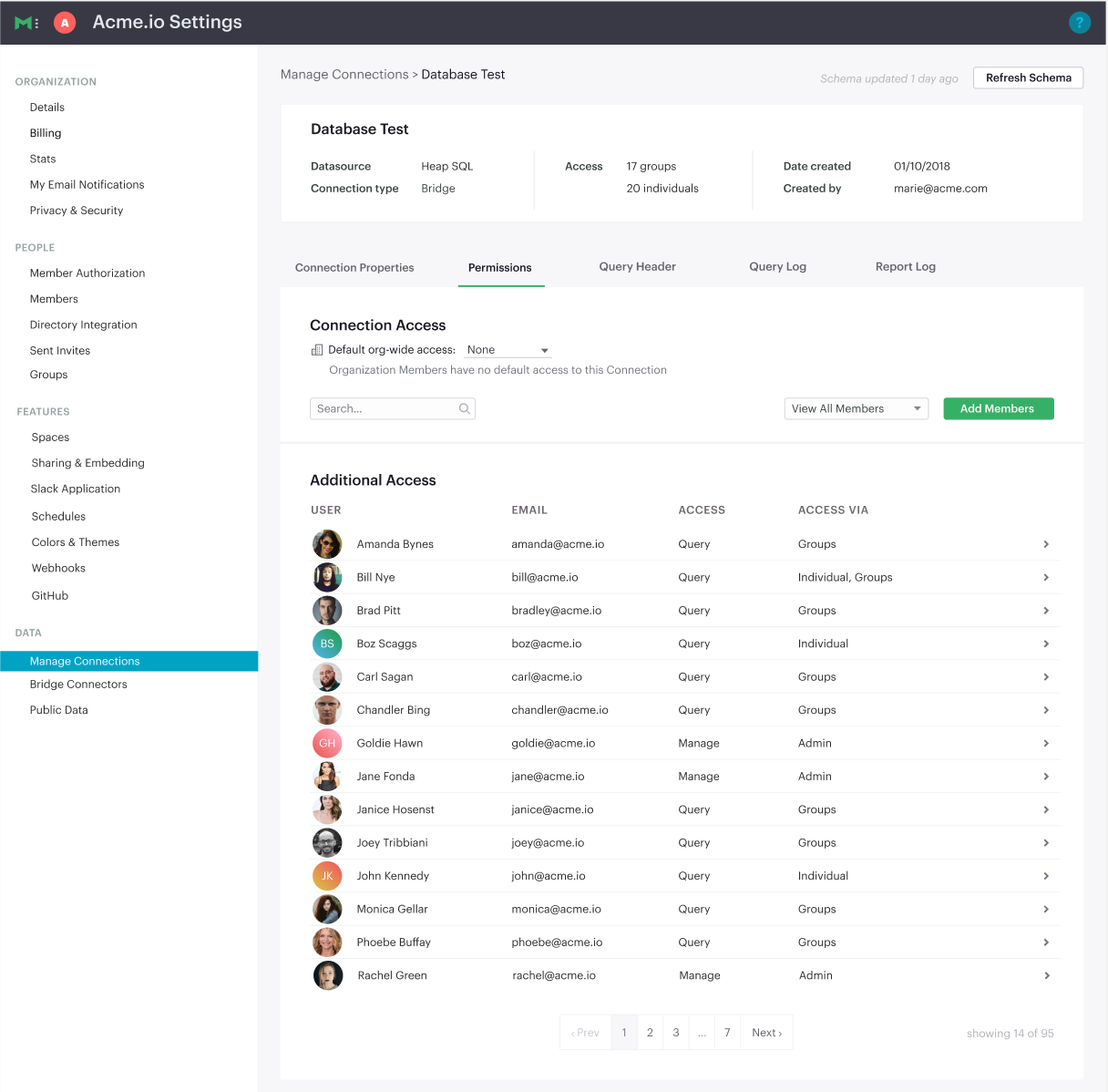
Access to a Connection determines a user’s ability to query and view data in Mode. Manage access to Connections by navigating to Workspace Settings, clicking into the Manage Connections tab, selecting a Connection and clicking the Permissions tab.
View Current Connection Access
For each Connection, you will see the default org-wide access at the top. This is the access that every member of your Workspace has to the Connection by default. Below that, you will see a list of users with additional access, along with their access level and how they got that access — they can have access via Group permissions, individual permissions or their status as an Admin. Use the filter dropdowns to show a list of individual users or Groups with access to the Connection.
Manage Connection Permissions
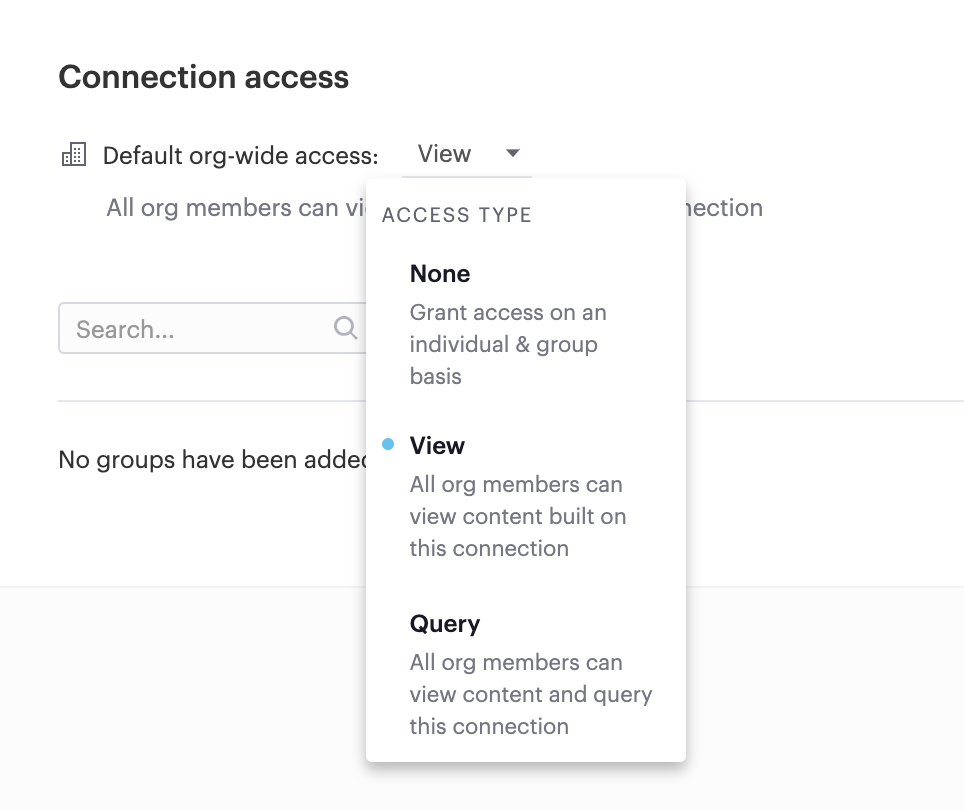
Manage the default access level for the Connection by updating the setting to None, View or Query.
To grant permissions for individuals and Groups in addition to the default access, use the Add members button. This will surface the modal shown below.
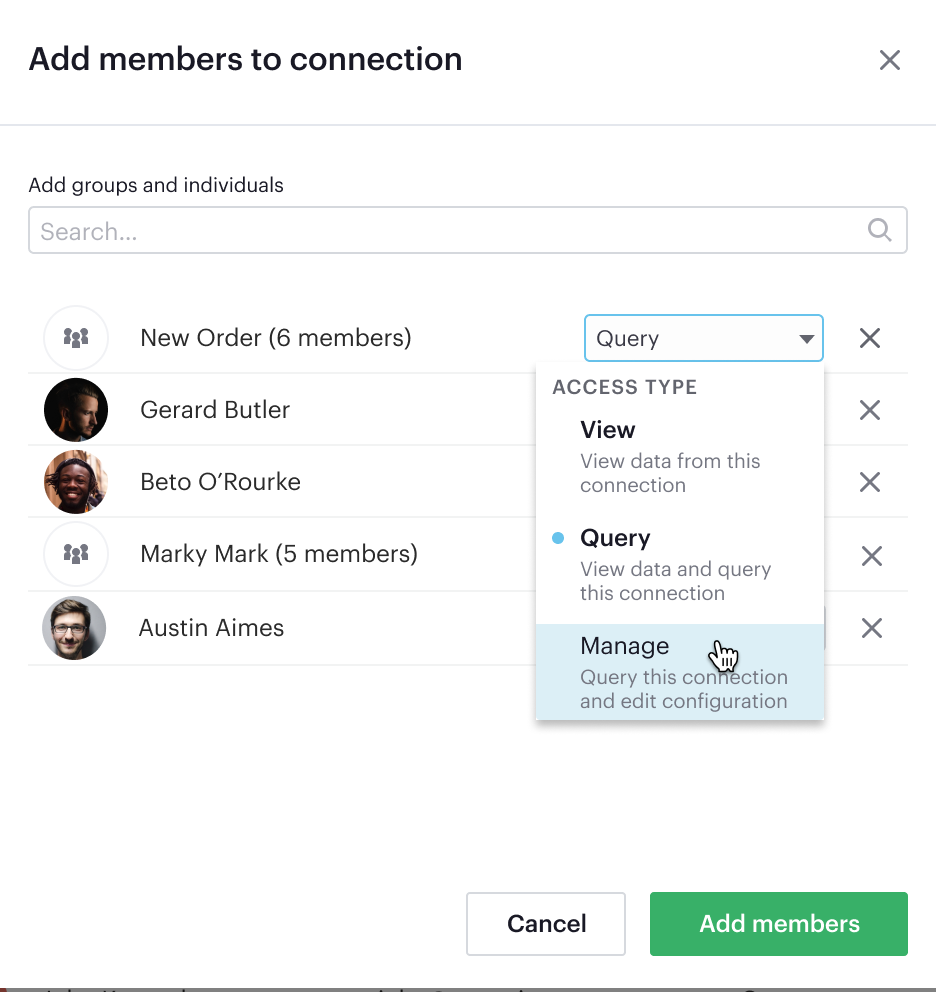
There are three types of permissions that can be granted to an individual or Group: Manage, Query or View.
- The Manage permission allows users to manage Connection settings without making them an Admin. This includes managing permissions. Only grant the Manage permission to non-Admin users who should be able to change permissions or settings for the Connection.
- The Query permission allows users to write & modify queries against the Connection. Only users with this permission can create and edit Reports using this Connection.
- The View permission allows users to view Reports created using the Connection. This includes the ability to use parameters and run Reports.
Set up Collection Permissions
Use Collections to organize and manage access to Dataset and Reports in your Mode Workspace.
When you create a new Dataset or Report, it is private to you. Your Personal content is accessible via the link, but cannot be found via search or navigation in Mode until moved into a shared Collection.
In order to move a Dataset or Report into a Collection, you must have Edit permission for the destination Collection. Moving a Dataset or Report may also change who has access to it. You can see the default access for a Collection in the interface when you choose to move a Dataset or Report, to understand whether Workspace members may lose access.
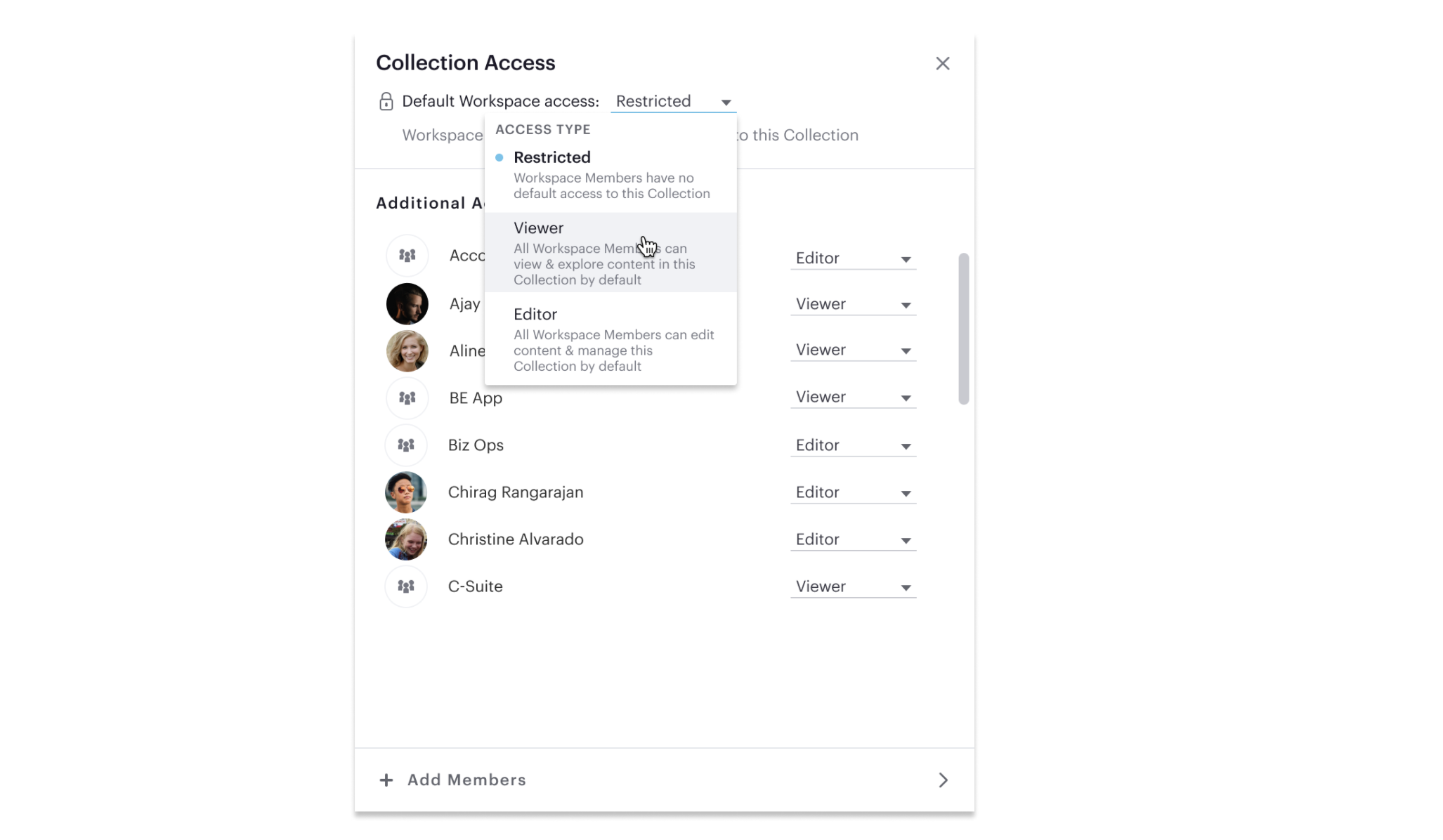
Setting Default Workspace Access
When creating a new Collection, you’ll have to set the default access to that Collection. Default access is the level of access that all Workspace members will have to Reports and Datasets in that Collection. There are three options for the Workspace default access level for a given Collection.
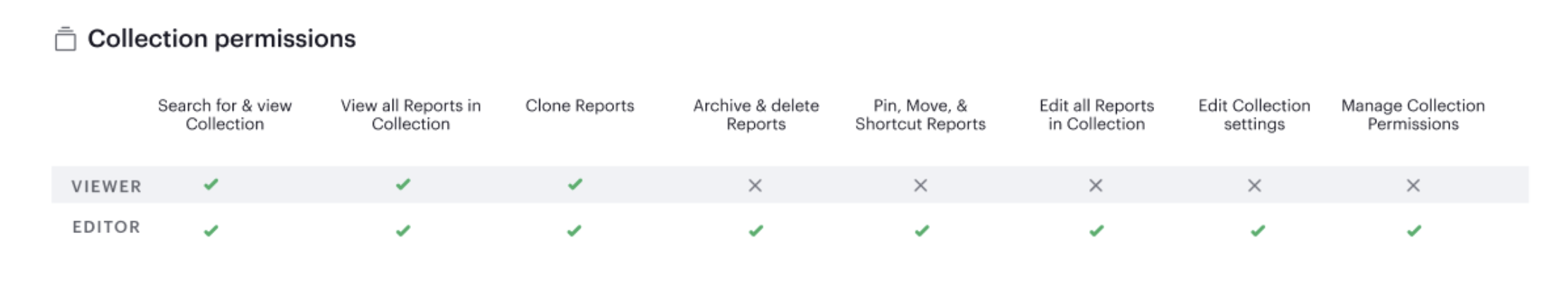
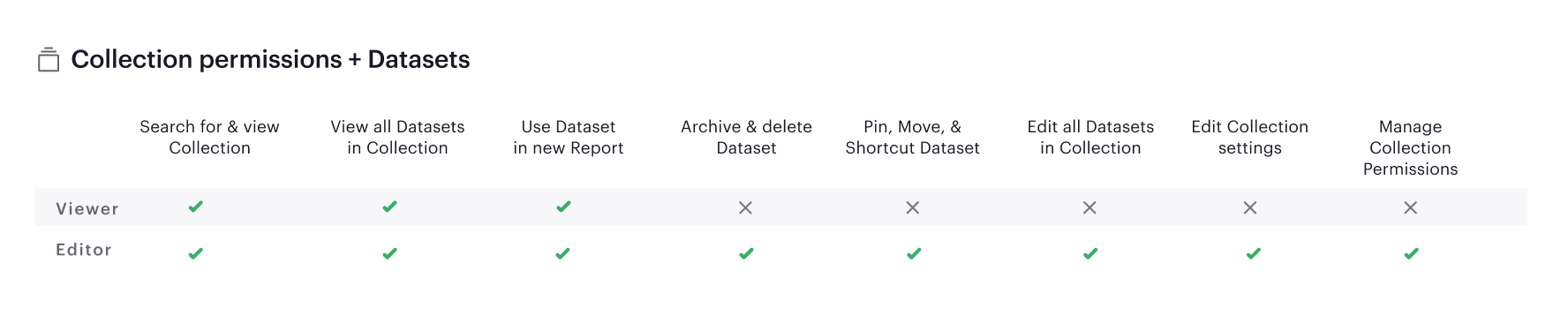
Setting the default to Restricted means that Workspace members have no access to the Collection by default. Viewer grants all Workspace members the ability to view Reports and Datasets in the Collection. For Datasets, this means viewers can also create new Reports from the Dataset. For Reports, this means viewers can also create Explorations based on those Reports.
Editor grants all Workspace members the ability to edit the Reports or Datasets (and their underlying SQL queries) contained in that Collection.
The chart below shows what actions Viewers & Editors can take.
Manage Collection Permissions
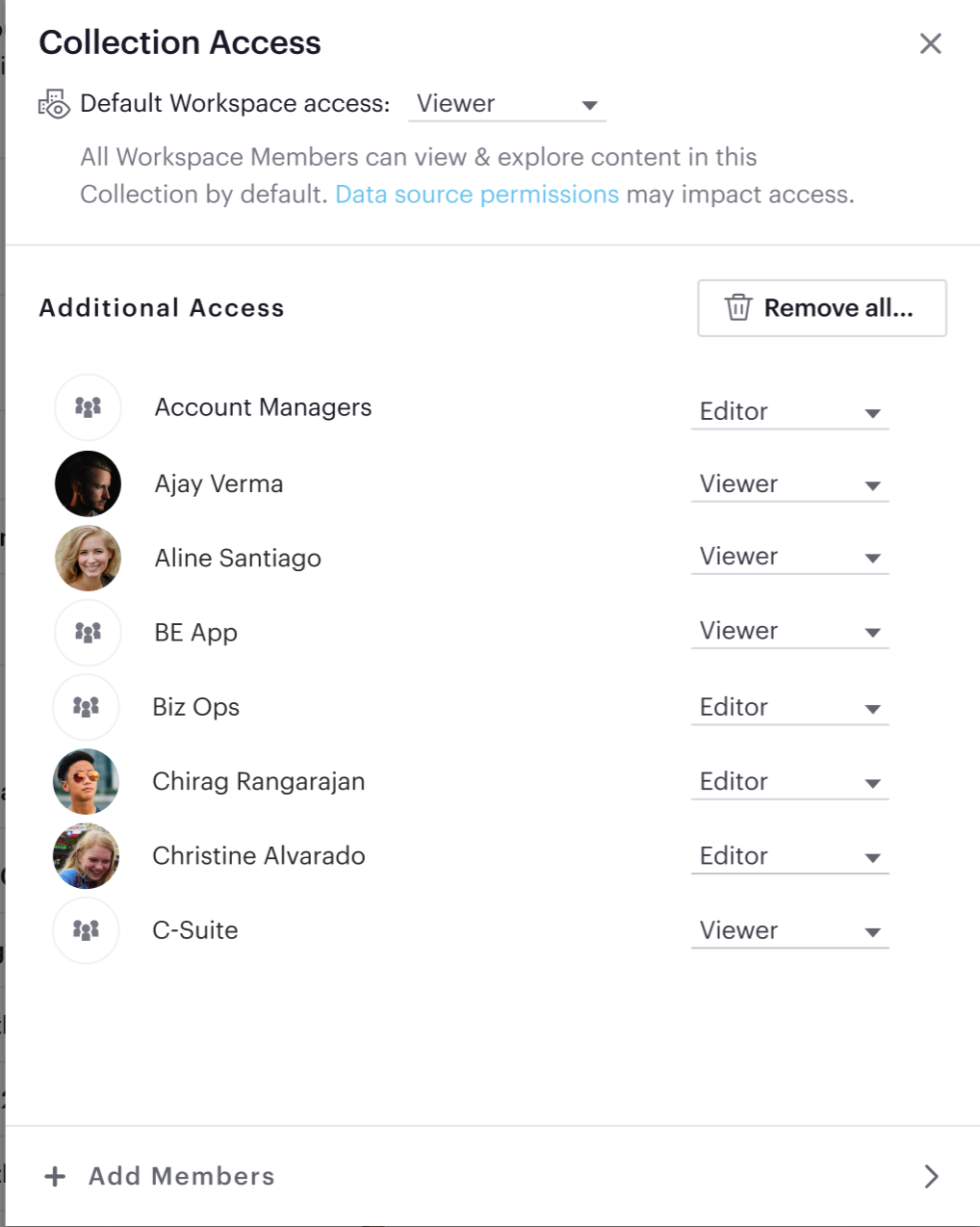
Once default Workspace access is set, you’ll have the chance to grant additional access via the Manage Access modal. (This screen will show automatically when you create a new Collection, and you can access it any time by clicking the gear icon to the right of the Collection name. You can also access this modal from the My Collections view to manage Collection permissions in bulk.)
To add Group or individual access to the Collection, select Add Members and search for and select individuals or Groups to grant access.
From the Manage Access modal, you can also update the default Workspace access at any time.
Admins can bulk remove additional access to a Collection by clicking the Remove all... button. This action is only available to Admins and completely resets permissions to the Collection. Once access is removed it cannot be reverted.
Permissions Best Practices
- Encourage fellow Workspace members to use Collections to organize Reports. Move Personal Reports into Collections to share them with other users. For example, if you want to collaborate on draft work, create a Collection for drafts and grant edit access only to the subset of users or Groups you want to collaborate with.
- Create Collections that map to your business needs. For example, you can set up Collections to organize Reports by business unit. Another common use case is creating a Collection for company-wide KPI reports, setting the default Workspace access to Viewer (so everyone can view and create Explorations), and adding the Data Science Group with Edit permissions.
- Use Groups to streamline setting up permissions for Collections. For example, if you set the default access for the Marketing Collection to be Viewer, but you want to grant all members of the Marketing team access to edit Reports in this Collection, create a Marketing group and grant that group Editor permissions.
- Set the default access for Collections that should be accessible to your entire workspace to Viewer. Only set the default access for a Collection to Restricted if the Collection contains Reports with sensitive data or data that should be restricted to a certain Group or individual users.
FAQs
Q: How do Collection and Connection permissions determine Report access for users?
To access a report, users must possess the necessary permissions for both the Connections utilized in the report, as well as for the Collection that holds the report. For instance, even if a user has been granted view permission for all of the Connections used in a report, if they are not a member of the private Collection containing the report, they will not be able to view the report. In other words, access to both the Connections and the Collection is required.
Q: What will users see if they don’t have access to view or edit a Report I share with them?
If users do not have access to view a Report, they will see a screen with the message below:
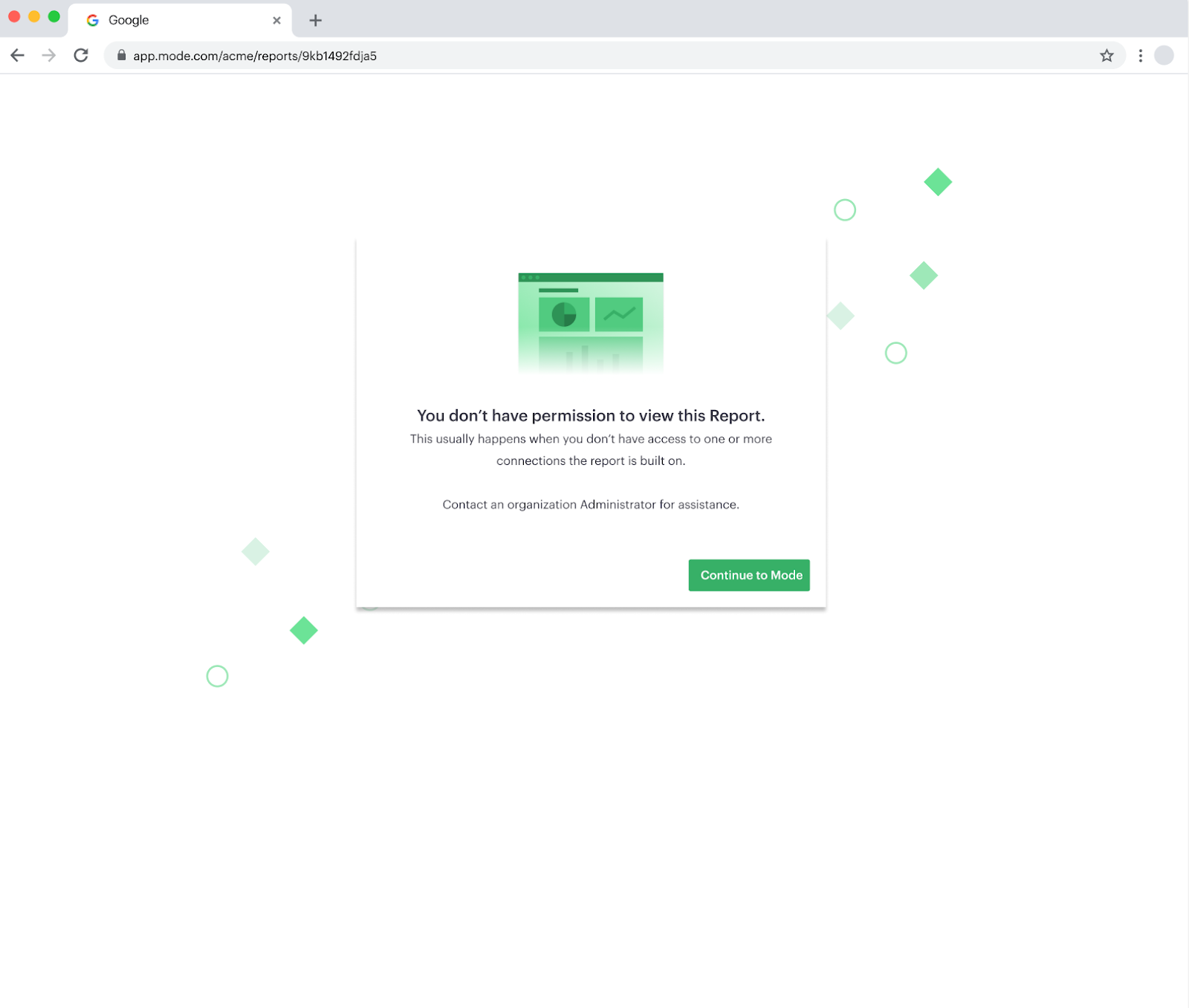 If users do not have access to edit a Report, they will be able to view the Report, without the link to take them to the editor. Users with view access can still run the Report and subscribe to existing schedules. They cannot create new schedules.
If users do not have access to edit a Report, they will be able to view the Report, without the link to take them to the editor. Users with view access can still run the Report and subscribe to existing schedules. They cannot create new schedules.
Q: If the Connection default access is set to “None,” only 1 user has “Query” permission, and they create a Report in a public Collection, would anyone be able to see it or edit it?
If default access is None, only users who have been granted access will be able to take the associated actions.
- Query: Write queries against Connection, edit & create Reports using the Connection
- View: View and explore Reports created on that Connection
If only one user has Query permission to the Connection, all other users will be able to view the Report but they will not be able to edit the Report.
Q: How can I allow a group of users to access a specific schema?
Mode will essentially maintain the permissions that you set in your native database. Therefore, since Mode connects to your database as a database user, if you established these permissions for a certain user and you use those user credentials to connect to a data source in Mode, those permissions will persists.
If you would like to group certain Mode users together to access a connection. You can read more about this here.
Was this article helpful?